Cryptanalysis Unveiled: Overview & Attack Types
Table of Contents
- jaro education
- 24, August 2023
- 3:00 pm
Cryptanalysis is a field of study and practice that involves analysing and decrypting ciphers, codes, and encrypted text without access to the correct key. Its primary objective is to gain access to the plain text content of a communication, even in the absence of the decryption key. Cryptanalysis experts dedicate their efforts to comprehending the inner workings of ciphers, cryptosystems, and ciphertext to understand their mechanisms. With this understanding, they strive to develop techniques to weaken or defeat them.
It is worth noting that cryptographers develop encryption codes used in cybersecurity, while cryptanalysts focus on breaking those encryption codes. These two roles represent opposing sides within cybersecurity, engaged in a perpetual conflict where each side endeavours to outwit the other. This ongoing competition serves as a driving force for innovation within cybersecurity. The article will give you a complete idea about what is cryptanalysis, how this concept is continuously updating.
The frequency of cyber dangers and crimes is continuously rising in today’s technological age. Individuals interested in decoding such offences should take up the Executive Programme in Cyber Security for Organisations by IIM Indore to handle these pressing concerns effectively. This programme aims to provide participants with a thorough awareness of cybersecurity. It serves people from various disciplines, including managers and professionals looking to develop careers in this industry. The course material covers many topics, including threat intelligence, risk management, incident response, network security, and security policy and postures integral to success in this field.
Use of Cryptanalysis
It is not surprising that hackers utilise cryptanalysis as part of their activities. Potential hackers employ cryptanalysis to identify cryptosystem vulnerabilities, opting for this approach instead of brute force attacks. Governments also employ cryptanalysis to decrypt the encrypted messages of other nations. Furthermore, companies specialising in cybersecurity products and services use cryptanalysis to assess the effectiveness of their security features. Even academia engages in cryptanalysis, with researchers and scholars actively searching for cryptographic algorithms and protocol weaknesses.
It is important to note that black-hat hackers, who engage in malicious cyber activities, and white-hat hackers, who conduct authorised penetration testing, use cryptanalysis. Black-hat hackers use it to carry out cybercrimes, while white-hat hackers employ it under the guidance of organisations that hire them to test their security measures.
Various Types of Cryptanalytic Attacks
The types of cryptanalytic attacks are as follows:
Man-In-The-Middle Attack
In this type of cyberattack, the attacker captures communication between two parties across a secure channel. The attacker can then listen in on, change, or tamper with the conversation between the participants
Chosen-Plaintext Analysis
The intruder selects particular plaintexts and obtains the appropriate ciphertexts in this attack. Studying these pairs and determining the encryption key is the goal. Despite being simple to implement, it occasionally has a low success rate.
Adaptive Chosen-Plaintext Analysis
It is similar to CPA but with an additional step. After obtaining ciphertexts for some plaintexts, the attacker requests more ciphertexts for additional plaintexts. This attack allows the attacker to adapt and refine their analysis based on the obtained information.
Birthday Attack
This attack exploits the probability of collisions in a hash function by finding two or more inputs that produce the same hash value.
Known-Plaintext Analysis
The attacker has access to some plaintext-ciphertext pairs and uses them to deduce the encryption key. This attack is relatively easier to execute since much information is already known.
Chosen-Plaintext Analysis
The intruder selects particular plaintexts and obtains the appropriate cipher texts in this attack. Studying these pairs and determining the encryption key is the goal. Despite being simple to implement, it occasionally has a low success rate.
Ciphertext-Only Analysis
The attacker only has access to the ciphertexts and tries to deduce both the encryption key and the corresponding plaintext. This type of attack is the most challenging to execute, as only the ciphertext is available for analysis.
Side-Channel Attack
Instead of directly targeting algorithmic flaws, this attack makes use of data gathered from the physical implementation of a cryptographic system, such as timing, power usage, or electromagnetic emanations.
Brute-Force Attack
This attack systematically tries all possible keys until the correct one is found. It can be time-consuming and computationally expensive, especially for longer keys.
Differential Cryptanalysis
This attack compares pairs of plaintexts and their corresponding ciphertexts to identify patterns in the encryption algorithm, particularly effective against block ciphers with specific properties.
These attacks demonstrate the various techniques employed to analyse and exploit cryptographic systems.
Tools Used in Cryptanalysis
There are several tools used in cryptanalysis. Here are some examples:
Cryptol
It is an open-source software designed for cryptanalysis, initially developed by the National Security Agency of the United States. It allows the users to analyse and monitor the operations of cryptographic algorithms. With its help, users can create programs that specify ciphers or algorithms and observe how they function.
CrypTool
It provides e-learning programs and a web portal for users to learn about cryptographic algorithms and cryptanalysis techniques. It also offers a hands-on approach to understanding cryptographic methods and allows users to experiment with and analyse different algorithms.
Ganzua
This tool allows analysts to define cipher and plain alphabets flexibly and is customisable. It is beneficial for cracking non-English cryptograms and supports analysing a wide range of cryptographic systems.
These are just a few names of the many tools available for cryptanalysis. Cryptanalysis constantly evolves, and new tools and techniques are developed for more accurate analysis and decryption of cryptographic systems.
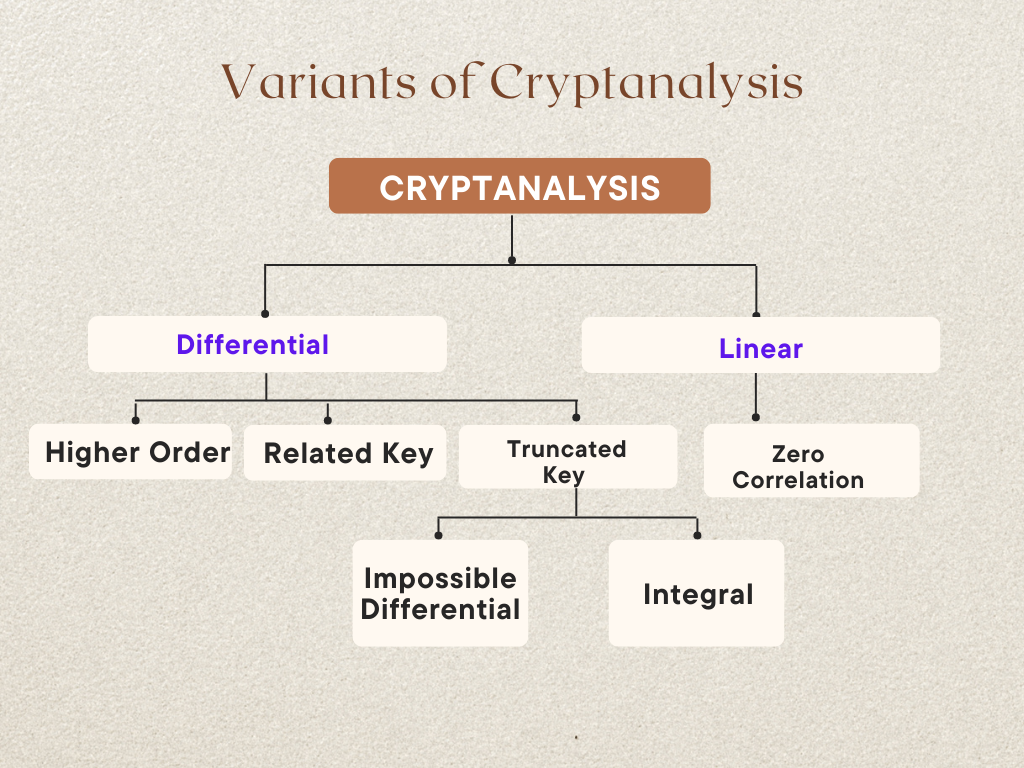
Forms of Cryptanalysis
There are two primary forms of cryptanalysis commonly used by analysts:
Linear Cryptanalysis
Linear cryptanalysis is a known plaintext attack discovering affine approximations to the target cipher’s operation. The attacker studies the probabilistic linear relationships, known as linear approximations, between the plaintext parity bits, ciphertext, and the secret key of the target cipher. This attack is frequently employed against block ciphers and is one of the most prevalent techniques.
Differential Cryptanalysis
This attack is effective against stream and block ciphers. In the case of block ciphers, it involves employing various strategies to track differences across a network of transformations. The goal is to identify instances where the cipher exhibits non-random behaviour and utilise these characteristics to deduce the secret cipher key. It examines how changes in the input information can impact the resulting differences in the output. Further, it analyses the propagation of differences through the cryptographic algorithm to gain insights into the encryption process.
These two forms of cryptanalysis provide analysts with powerful techniques to analyse and exploit cryptographic systems in block ciphers and stream ciphers. By understanding ciphers’ linear and differential properties, analysts can uncover vulnerabilities and weaknesses in encryption algorithms.
Duties and Qualification Requirements of Cryptanalysts
To become a cryptanalyst, one has to obtain a bachelor’s degree in computer engineering, computer science or a related field. While some organisations may consider candidates without a technical degree but with extensive training and experience in the field, relevant certifications in cybersecurity can be beneficial.
If someone is pursuing an academic path, a Master of Science degree is highly recommended, especially for those without a bachelor’s degree in mathematics and computer science. The ideal candidates may even hold a doctoral degree in computer science or mathematics, specialising in cryptography.
As a cryptanalyst, your responsibilities will involve developing algorithms, ciphers, and security systems to encrypt sensitive data. You will also be responsible for analysing and decrypting various forms of confidential information within cryptographic security systems, including encrypted data, ciphertexts, and telecommunications protocols.
Some essential duties include:
- Designing the security systems to identify and prevent vulnerabilities.
- Safeguarding critical sensitive information from interception, unauthorised copying, alteration, or deletion.
- Evaluating and analysing vulnerabilities in cryptographic security systems and algorithms employed within your organisation.
- Conducting investigations to identify weaknesses in communication lines.
- Testing computational models for accuracy and reliability.
- Developing statistical and mathematical models for data analysis with resolving security issues.
- Informed about the latest theories and applications in cryptology and testing them.
- Developing new methods of data encryption.
- Ensuring that financial data is appropriately encrypted and accessible only to authorised users within the organisation.
- Securing message transmission to prevent unauthorised access or alteration during transit.
These responsibilities highlight the importance of a cryptanalyst in maintaining the integrity and security of encrypted data and communications within an organisation.
Conclusion
Most modern encryption algorithms are designed to be secure against known attacks, and breaking them requires a deep understanding of advanced mathematics and complex techniques. However, straightforward methods can easily compromise older encryption and encoding algorithms. This knowledge becomes particularly valuable in cybersecurity because many malware variants rely on these weaker forms of encryption. A grasp of fundamental cryptanalytic concepts and techniques can be immensely beneficial in effectively countering such threats.
With IIM Indore’s Executive Programme in Cyber Security for Organisations, you can gain extensive knowledge of cybersecurity. This diverse training covers subjects including security policy, network security, threat intelligence, and more. Register with Jaro Education and learn from subject-matter experts, get practical knowledge, and create meaningful interactions